How golden sample authentication and lifecycle intelligence help prove authenticity
Aerospace and defense programs are designed to operate for decades. The electronics inside them are not.
That mismatch has quietly become one of the most persistent threats to program stability. Component lifecycles keep shrinking, supply chains keep fragmenting, and the open market continues to expand as an unavoidable sourcing channel. The result is a risk environment where counterfeit exposure is no longer a rare exception. It is a predictable outcome of long-life systems operating in short-life electronics markets.
The counterfeit problem is often framed as a procurement issue. In reality, it is a lifecycle issue. It begins long before a buyer is forced to source an obsolete component. It begins when teams design systems without the verification infrastructure needed to sustain them.
Accuris data shows an average of 89 electronic components go obsolete every day. That is nearly 32,500 parts per year disappearing from authorized channels. Scarcity increases sourcing pressure, and sourcing pressure increases counterfeit risk.
But the deeper issue is not simply obsolescence. It is confidence.
When teams cannot reliably authenticate electronic components, every sourcing decision carries hidden exposure: performance drift, reliability failures, traceability gaps, qualification risk, warranty uncertainty, and even cybersecurity implications. Counterfeit mitigation, then, is not only about catching bad parts. It is about building a repeatable way to prove authenticity when the supply environment becomes unpredictable.
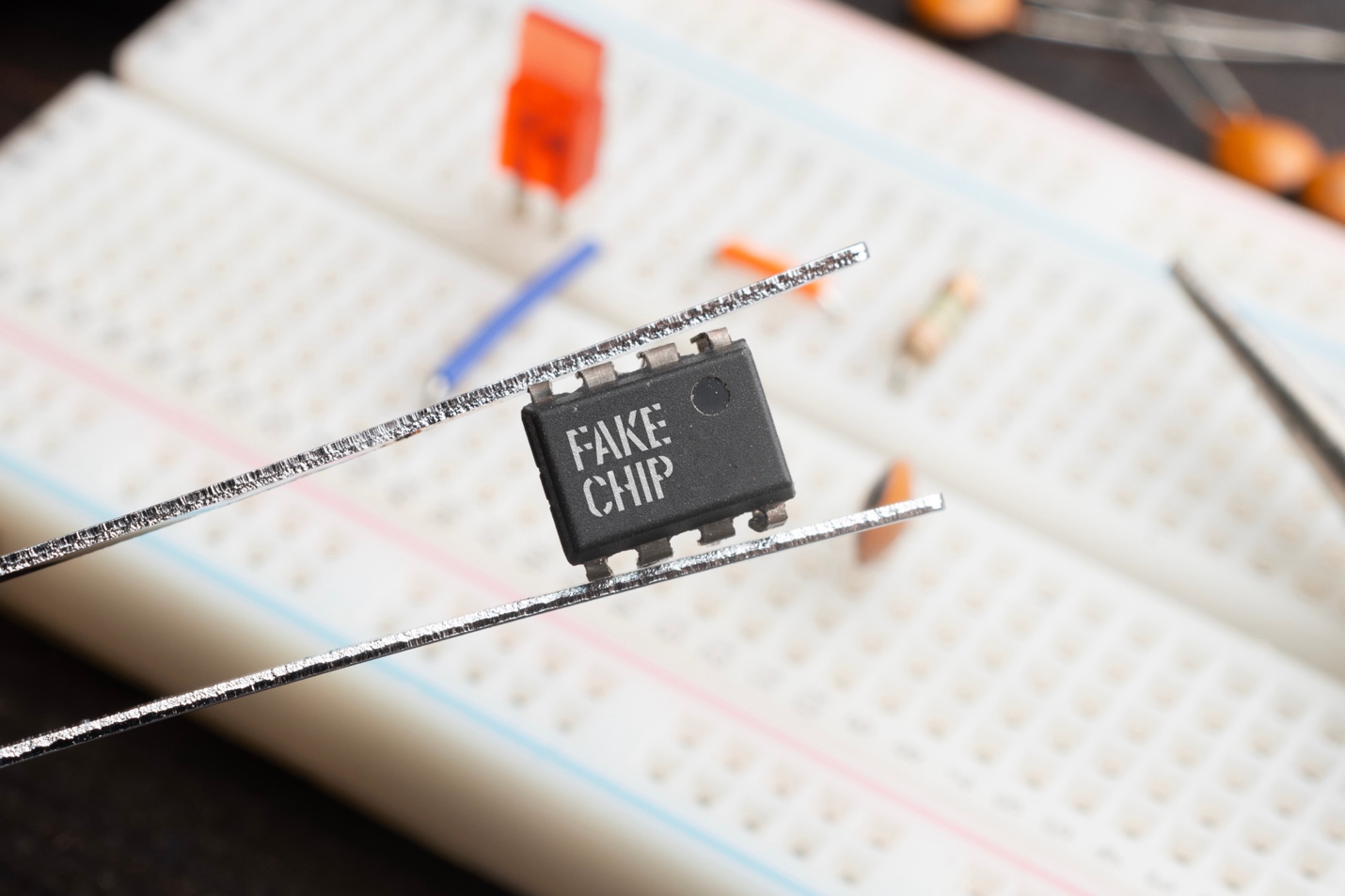
The hidden reality: authentic parts do not always look consistent
One of the most overlooked challenges in counterfeit detection is that real components can vary in ways that are difficult to interpret without context.
Parts may ship years after original release. Manufacturing materials may shift based on availability. Suppliers may re-grade or remark components to meet market demands. Each of these is explainable in isolation. Together, they create a reality where the visual and physical signals engineers once relied on are less reliable than they appear.
This creates a dangerous decision environment. A component can look “wrong” but be authentic. Or it can look correct and still be counterfeit. In both cases, teams are forced into judgment calls that are difficult to defend in audits, investigations, or failure analysis.
The goal is not to eliminate all variation. The goal is to separate normal variation from unacceptable deviation, and to do so with defensible evidence.
Why the open market concentrates counterfeit risk
As components move toward end of life, more organizations are forced to source through independent distributors and open-market channels. That is where counterfeit risk concentrates, and not only because counterfeiters operate there. Risk concentrates because the operating constraints are different.
Return windows are short. Disputes may be controlled by the seller. Authentication timelines often exceed the window in which parts can be rejected. Even when testing is performed, the Device Under Test approach may still fall short of full confidence.
In the open market, teams are frequently asked to make high-stakes decisions under time pressure with incomplete information. This is how counterfeit parts slip through. Not because teams do not care, but because the system was never built to support certainty.
The reference problem: without an exemplar, you are guessing

Most counterfeit mitigation methods focus on detection. Inspection. Testing. Standards-based workflows. These are necessary, but they are not sufficient.
The fundamental challenge is that counterfeit detection is a comparison problem. If you do not know what “good” looks like, you cannot reliably identify what is “bad.”
This is where many programs struggle. External inspection can validate packaging, markings, and surface-level characteristics. But counterfeit risk increasingly includes deeper substitutions that are not visible without reference data. Die-level differences, internal construction changes, and subtle revision mismatches can all evade surface checks.
Without a verified exemplar, teams are left with assumptions. That is not a strategy. It is a gamble.
Golden samples: building authenticity into the lifecycle
Golden samples, also referred to as verified exemplars, solve the reference problem by establishing a known-good baseline. They are authentic reference components captured under controlled conditions and retained for future comparison.
Golden samples matter because they preserve verification confidence across time. They remain valuable when authorized inventory disappears, when revisions shift, and when open-market sourcing becomes unavoidable.
More importantly, golden samples change the economics of counterfeit mitigation. They reduce the need for repeated exploratory investigation and increase the repeatability of verification workflows. They make it easier to escalate discrepancies quickly and objectively. They provide audit-ready proof that decisions were grounded in evidence, not assumption.
A strong golden sample program also shifts counterfeit mitigation earlier in the lifecycle, when options are broader and costs are lower.
Why proactive mitigation starts in development
Most organizations treat counterfeit mitigation as something that begins after risk appears. After a part becomes scarce. After a supplier fails. After a quality event. By then, the program is already paying the penalty.
A lifecycle approach reframes the timeline. The highest-leverage moment is development. That is when teams can still choose parts strategically, document alternates, evaluate supply chain exposure, and capture golden samples while authorized inventory is abundant.
Production is the phase where counterfeit risk becomes expensive. Line stoppages, requalification work, delayed shipments, and troubleshooting consume time and budget. End of life is the phase where counterfeit risk becomes structural. With no verified baseline, programs lose the ability to authenticate with confidence and redesign becomes the default response.
Golden samples are not a reaction tool. They are a design output. They are the bridge between engineering intent and sustainment reality.
Lifecycle intelligence makes golden samples actionable
Golden samples alone are not enough if teams cannot deploy them operationally.
The difference between a useful golden sample program and an unusable one is accessibility, traceability, and workflow integration. Teams need to know which components are high risk. They need lifecycle visibility across the BOM. They need the ability to request, catalog, and compare reference data without turning the process into a manual burden.
This is where lifecycle intelligence becomes essential. When programs can routinely run BOM lifecycle checks, identify at-risk components, and connect those risks to authentication readiness, golden samples become proactive rather than reactive.
The result is a verification system that scales.
The business case: counterfeits are not just technical failures

Counterfeit events create technical failure risk, but their impact is broader.
Investigation logistics, requalification testing, field replacement, downtime, and reputational damage can turn a single counterfeit incident into a major financial event. The defense and aerospace sector estimate places the average cost at $700K per event.
And cost is only one side of the equation. Compliance demands proof. Aerospace and defense programs operate under standards and requirements such as AS9100, AS5553, AS6171, and DFARS obligations that expect organizations to demonstrate counterfeit avoidance controls and traceability.
A program that cannot prove authenticity is exposed even when no failure has occurred. In modern supply chains, the absence of proof is itself a risk.
A practical path forward
Counterfeit mitigation does not require perfection. It requires preparedness.
The programs that manage counterfeit risk best do not rely on hope or heroic inspection. They build repeatable systems:
They run lifecycle checks routinely. They identify which components are most likely to create open-market exposure. They catalog golden samples for critical EEE components while authorized inventory exists. They build verification into receiving and sustaining workflows. And they maintain traceability so that authenticity decisions can be defended when scrutiny arrives.
Counterfeit risk is not going away. Obsolescence is accelerating. Open-market sourcing will continue to be part of the reality for long-life systems.
The question is whether organizations will continue to treat authentication as a reactive scramble, or whether they will build verification confidence into the lifecycle from the start.
Get started with a counterfeit detection strategy
Understanding the drivers of counterfeit risk is the first step; knowing how to act on them is what makes the difference.
Our on-demand webinar Eliminating Counterfeit Risks in Aerospace & Defense expands on the sources of risk and practical approaches to authentication.
After watching, use BOM lifecycle intelligence to flag high-risk components and integrate golden sample authentication into your verification processes.
Get started at Accuris.com/BOM.